Keeping your wallet backup safe
Your Trezor hardware wallet will create and store your keys safely offline. This keeps you safe from remote attacks, and your (formerly recovery seed) protects your keys even if your Trezor gets damaged. Keeping your wallet backup safe in the long run may seem like a daunting task, so here’s some tips to help you choose a safe place for your wallet backups.
Define your threat model
Before getting too worked up about the potential risks facing your Bitcoin, take a moment to assess the most probable threats you face. It is important to understand that everyone has a different threat model, and this can change over time.
Environmental risks
Environmental threats like sunlight, fire or water might damage your wallet backup, depending on the material it was recorded on. For instance, we have reports of accidents, during which a house burned down, lost in the aftermath of hurricanes, or the wallet backup was accidentally thrown out.
Physical attacks
A person holding 100 Bitcoin in their Trezor will be a much more desirable target than someone holding a few million sats, but only if the amount is known. Simply being outspoken about owning Bitcoin can put you at risk, no matter how much you own.
It may seem trivial to talk about owning a small amount right now, but the value could increase, or a potential attacker may simply jump to their own conclusions. By keeping a low profile, you are far less likely to find yourself under threat.
Addressing the physical threat vector takes some discipline. A hardware wallet will stop a physical attacker from getting to your keys, but it’s best to never get into that situation. Don’t talk about how much Bitcoin you own, be careful with sharing other data, and secure your keys where only you can access them.
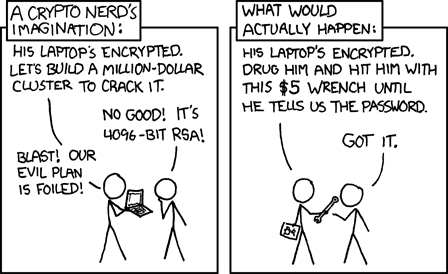
$5 wrench attack
The term "$5 wrench attack" describes a situation where an individual tries to force you to hand over your cryptocurrency assets by using threats of physical violence or death. In such scenarios, it is crucial to take steps to secure your assets and minimize the risk of losing them. This includes keeping the amount of your cryptocurrency holdings confidential and distributing your assets across multiple, separate storage locations.
One option for this is to use multiple hardware wallets, which are considered to be a secure method for storing cryptocurrency.
Remote attacks
The biggest threat most of us are vulnerable to is a remote attack, where an attacker will try to steal keys using malware or phishing over the internet. Physical theft is statistically much less common but still poses a risk to anyone identified as a worthwhile target.
Hardware wallets mitigate remote attacks by keeping your keys offline at all times. They also let you see exactly what you are signing, unmasking more sophisticated attacks. Starting to use a hardware wallet is the biggest security improvement you can make.
Writing down the wallet backup
By now you probably know that the wallet backup is a crucial element for the security of your Trezor hardware wallet.
If your device is lost, damaged or stolen, you can use your wallet backup to restore access to your entire wallet, passwords and other data associated with it.
The process is simple; you only have to enter the words of your wallet backup into your new Trezor device.
There is only one occasion when your Trezor will reveal your wallet backup, and that is during the backup procedure. Keep in mind that your Trezor will only show your wallet backup once.
When you first set up your Trezor, it will prompt you to run the backup process. Be extremely careful during this procedure, and make sure you copy the words from the device display carefully. Make sure the words are spelled correctly and are in the right order.
Please run the backup process alone.
Be aware of the environment around you; mind the various recording devices in your vicinity.
Please note that there might be a camera or a microphone on your computer or your phone.
Never store your wallet backup digitally.
Compared to physical media, digital media can be easily accessed. Digital copies can be made without the owner noticing until it is too late.
Do not read your wallet backup words out loud.
Choose a good material and keep your wallet backup card safe from environmental elements. For increased endurance, consider investing in a steel recovery wallet backup solution.
Storing a standard BIP39 wallet backup
Remember, your wallet backup is the single point of failure, and therefore must be kept well protected at all times.
There are two points to focus on when storing a wallet backup it must be stored somewhere only you can access, and it should be durable. The durability issue is commonly solved by engraving the wallet backup in a tough material, such as stainless steel or titanium, which will survive a disaster. Securing the backup is a more difficult task for the average person to manage.
There are pros and cons to each option for storing your wallet backup, so consider your threat model to decide on a solution that works for you.
You can learn more about BIP39 here.
Using a home safe
Storing your wallet backup in a hidden safe at your house is one of the only ways to control who has access to it. Seeing a safe is enough to raise the interest of any potential thief, so if using this storage method you should find a discreet place to install the safe, obscured from the view of guests, housemates or cleaners.
If there is a likelihood that your bitcoin holdings are known by others and somehow connected to your home address, this option may not be viable for you. A more flexible recovery method such as a Multi-share Backup might be more suitable, so even if the wallet backup in your safe were compromised your funds would remain protected.
If you have multiple wallets, it’s also possible to use them in a multisignature (multisig) setup, where each wallet acts as one key and the wallet backup for each can be held in different locations, meaning a compromised safe would not be so disastrous. This is more complex to set up than a Multi-share Backup, but offers advantages if custody of the funds are shared by multiple people.
A hidden location on your property
While not as secure as a hidden safe, you may have a hard-to-access and discreet location on your property where you can hide your wallet backup, such as a locked loft, or out of reach and out of sight somewhere in a locked room. There are many options, and you will need to assess the layout of your property to determine if there is any truly secure location to use.
Burying your wallet backup
Storing your recovery wallet backup underground is often referenced as an option, but there are several reasons it may be a bad idea. Many materials will degrade faster in a damp, acidic environment, so precautions have to be taken to transcribe the backup to a durable material and to limit exposure to dirt and humidity.
Another issue when burying a wallet backup outdoors is choosing a good location. You should be in control of who can access the land, and must take steps to prevent it from being uncovered accidentally, and to make sure you will remember where you left it.
Limitations of a wallet backup
While BIP39 wallet backups made it much easier to secure Bitcoin offline, they are still not ideal since they must be heavily protected and are a single point of failure that could lead to a loss of funds. You can take precautions against this by using SatoshiLabs' new standard called SLIP39. This backup method improves upon BIP39 and lets you securely generate multiple lists of words that must be combined in order to restore access to the funds.
Using SLIP39, there is redundancy that allows one or several lists to be lost or stolen without security being affected. This makes it simpler and safer for the average person to protect their wallet backup, even without access to highly secure storage solutions.
Using SLIP39
Wallet backups are widely used but can be problematic to secure. SLIP39 backup makes it easy to safely store a backup of your keys across multiple locations, lessening the risk of losing access to your Bitcoin through theft or damage.
SLIP39 is a feature available on the Trezor Safe 5, Trezor Safe 3 and Trezor Model T that lets you create up to 16 shares, where each share is a list of 20 words. You then choose a threshold, which sets how many shares are needed to recover the keys. With these two options, you can customize your setup in many ways to suit your threat model.
There are two configurations of Shamir backup that are most commonly used, known as two-of-three and three-of-five. The naming of these systems is formatted as 'threshold-of-total' shares, so the first scheme is three shares in total and a threshold of two shares needed for recovery. Three-of-five means five shares in total and any three needed for recovery.
It is best not to overcomplicate a Shamir backup. Unless you have a specific use case that needs any other configuration, it is best to stick with two-of-three or three-of-five setup. A two-of-three setup offers redundancy where one share can be lost, destroyed or stolen, while three-of-five allows two shares to be lost without affecting your funds.
Using Shamir backup means less paranoia and more practical physical security. While it’s good practice to keep shares locked away, with Shamir backup you can distribute your shares between your home, a relative’s house, your office, and so on; even if one location is compromised it does not impact your ability to recover your funds
Limitations of SLIP39
SLIP39 is a more robust solution than a BIP39 wallet backup, but it is not as widely supported as BIP39. That means to recover a wallet using Shamir backup you will need to use a Trezor Safe 5, Trezor Safe 3, Trezor Model T or one of the other third-party wallets that support the standard.
SLIP39 is open source, meaning we gave this standard to the community so anyone can use it, and we believe support of SLIP39 will continue to grow. Should Trezor cease to exist, there are open tools available to recover SLIP39 backups.
It’s also easy to be complacent with SLIP39, but you should still hide your shares securely to prevent someone from covertly tracking them down, and regularly check on the state of your shares in case they get damaged. While you may be able to lose several shares without endangering your funds, you must always have enough to meet the recovery threshold.
Choosing the right material for your wallet backups
Paper wallet backups, where you write down your wallet backup in pen or pencil, are susceptible to disasters such as fire or flood. As covered above, a BIP39 backup is a single point of failure, meaning if it gets destroyed and you lose your Trezor, you will never be able to recover your funds. Anyone using a 12 or 24-word wallet backup will benefit from engraving or punching their backup into a metal wallet backup, to offset the risk of disaster.
If you use a SLIP39 backup, the redundancy allowing for shares to be lost or damaged means a metal wallet backup might not offer significantly more protection. Depending on how you distribute the shares, you may choose to invest in several metal wallet backups where there is a higher risk of the share becoming damaged, for example if buried or kept somewhere that may not be possible to access for a long time.
Trezor Keep Metal
In 2023, we launched our new wallet backup storage solution, the Trezor Keep Metal, which provides a robust and environment-proof solution for storing your wallet backup. For more information, please watch this video: