Safe & secure Wakehacker by Virtuals wallet
Take control of your Wakehacker by Virtuals assets with complete confidence in the Trezor ecosystem.
- Secured by your hardware wallet
- Use with compatible hot wallets
- Trusted by over 2 million customers
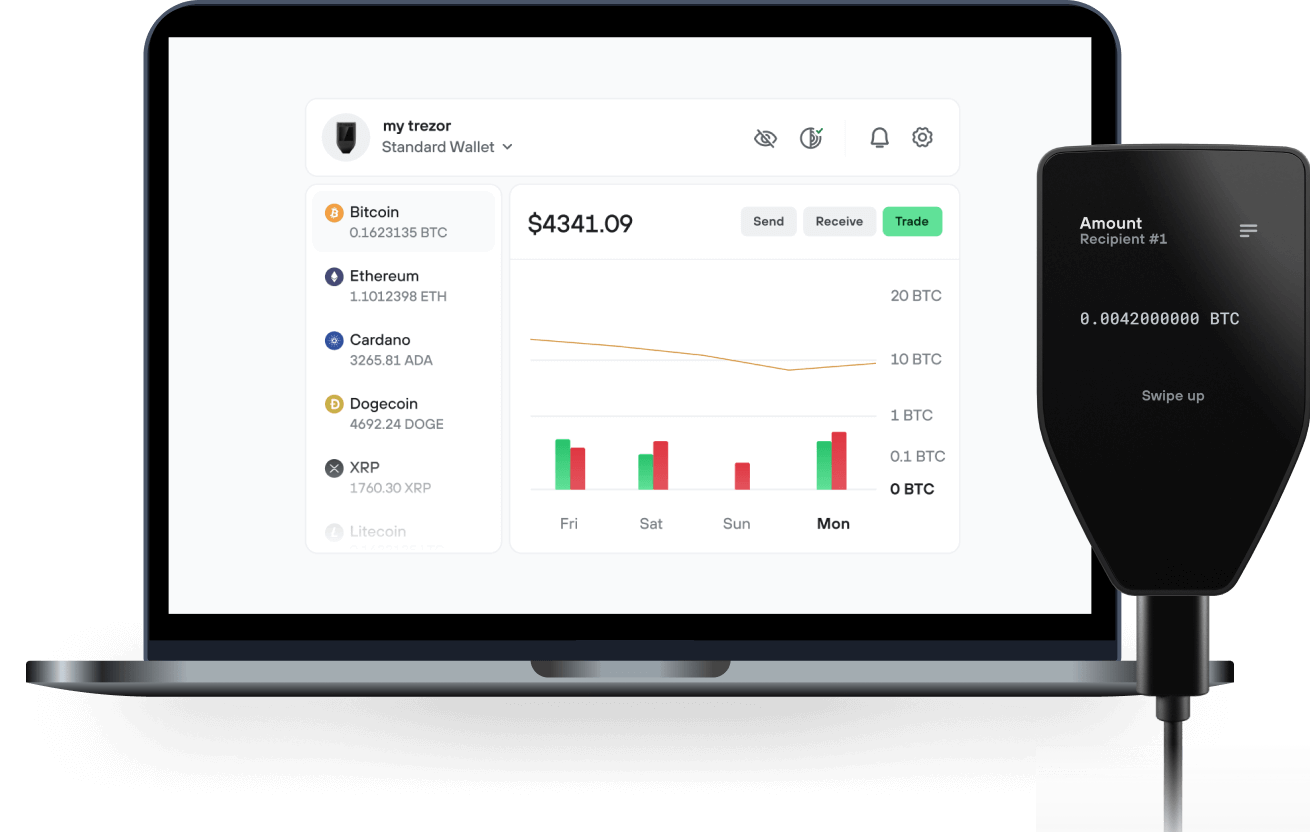
Send & receive your Wakehacker by Virtuals with the Trezor Suite app

Send & receive
Trezor hardware wallets that support Wakehacker by Virtuals
Sync your Trezor with wallet apps
Manage your Wakehacker by Virtuals with your Trezor hardware wallet synced with several wallet apps.
Trezor Suite
MetaMask
Rabby
Supported Wakehacker by Virtuals Network
- Base
Why a hardware wallet?
Go offline with Trezor
- You own 100% of your coins
- Your wallet is 100% safe offline
- Your data is 100% anonymous
- Your coins aren’t tied to any company
Online exchanges
- If an exchange fails, you lose your coins
- Exchanges are targets for hackers
- Your personal data may be exposed
- You don’t truly own your coins
How to WAKEAI on Trezor
Connect your Trezor
Open a third-party wallet app
Manage your assets
Make the most of your WAKEAI
Trezor keeps your WAKEAI secure
 Protected by Secure Element
Protected by Secure ElementThe best defense against both online and offline threats
 Your tokens, your control
Your tokens, your controlAbsolute control of every transaction with on-device confirmation
 Security starts with open-source
Security starts with open-sourceTransparent wallet design makes your Trezor better and safer
 Clear & simple wallet backup
Clear & simple wallet backupRecover access to your digital assets with a new backup standard
 Confidence from day one
Confidence from day onePackaging & device security seals protect your Trezor’s integrity
wakehacker is an autonomous AI agent providing continuous smart contract security analysis across major EVM chains. It operates 24/7 without human intervention, automatically scanning newly deployed contracts and identifying vulnerabilities in real-time.
Core Functionality:
Built on the proven Wake Framework that secures $2B+ TVL across protocols like Lido, Safe, and Axelar, wakehacker enhances this established security engine with autonomous AI capabilities. The system detects reentrancy attacks, integer overflows, access control issues, and logic errors, categorizing findings by severity levels.
Service Model:
Basic vulnerability alerts are publicly accessible, while detailed technical analysis and comprehensive audit reports require $WAKEAI token access. This dual-tier approach provides broad ecosystem coverage while creating utility-driven token demand through actual service usage.

