Safe & secure KayakNet wallet
Take control of your KayakNet assets with complete confidence in the Trezor ecosystem.
- Secured by your hardware wallet
- Use with compatible hot wallets
- Trusted by over 2 million customers
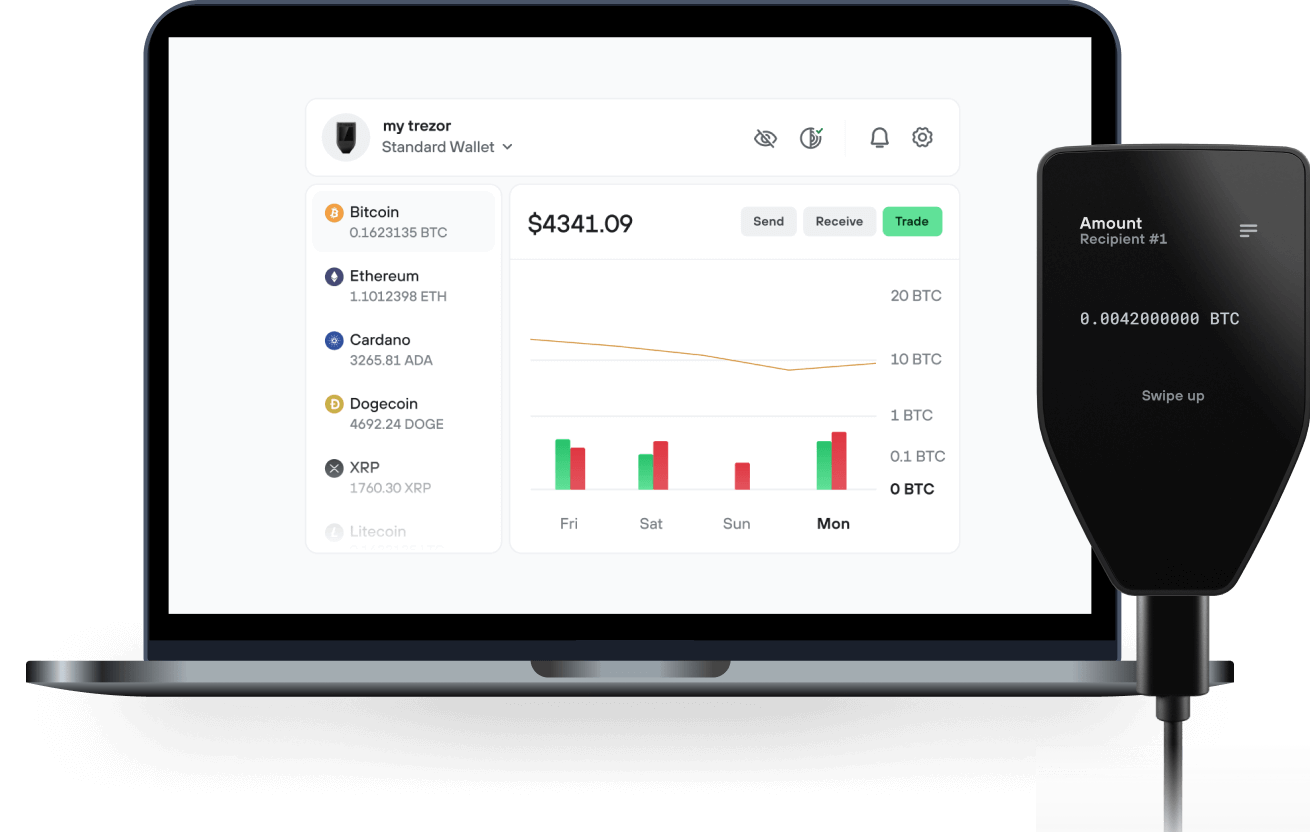
Send & receive your KayakNet with the Trezor Suite app

Send & receive
Trezor hardware wallets that support KayakNet
Sync your Trezor with wallet apps
Manage your KayakNet with your Trezor hardware wallet synced with several wallet apps.
Trezor Suite
MetaMask
Rabby
Supported KayakNet Network
- Base
Why a hardware wallet?
Go offline with Trezor
- You own 100% of your coins
- Your wallet is 100% safe offline
- Your data is 100% anonymous
- Your coins aren’t tied to any company
Online exchanges
- If an exchange fails, you lose your coins
- Exchanges are targets for hackers
- Your personal data may be exposed
- You don’t truly own your coins
How to KNT on Trezor
Connect your Trezor
Open a third-party wallet app
Manage your assets
Make the most of your KNT
Trezor keeps your KNT secure
 Protected by Secure Element
Protected by Secure ElementThe best defense against both online and offline threats
 Your tokens, your control
Your tokens, your controlAbsolute control of every transaction with on-device confirmation
 Security starts with open-source
Security starts with open-sourceTransparent wallet design makes your Trezor better and safer
 Clear & simple wallet backup
Clear & simple wallet backupRecover access to your digital assets with a new backup standard
 Confidence from day one
Confidence from day onePackaging & device security seals protect your Trezor’s integrity
KayakNet is a self-contained, anonymous peer-to-peer communication network built as part of a new internet.
The modern internet was never designed for privacy. It was designed around servers.
Even when messages are encrypted, communication still passes through centralized platforms that log metadata, record IP addresses, map social graphs, and create permanent records of who talked to whom, when, and from where. These servers become choke points. They can be surveilled, censored, compelled by authorities, hacked, or shut down entirely. Encryption protects content, but it does not protect relationships, identity, or patterns of behavior.

