Safe & secure ZKEncrypt AI wallet
Take control of your ZKEncrypt AI assets with complete confidence in the Trezor ecosystem.
- Secured by your hardware wallet
- Use with compatible hot wallets
- Trusted by over 2 million customers
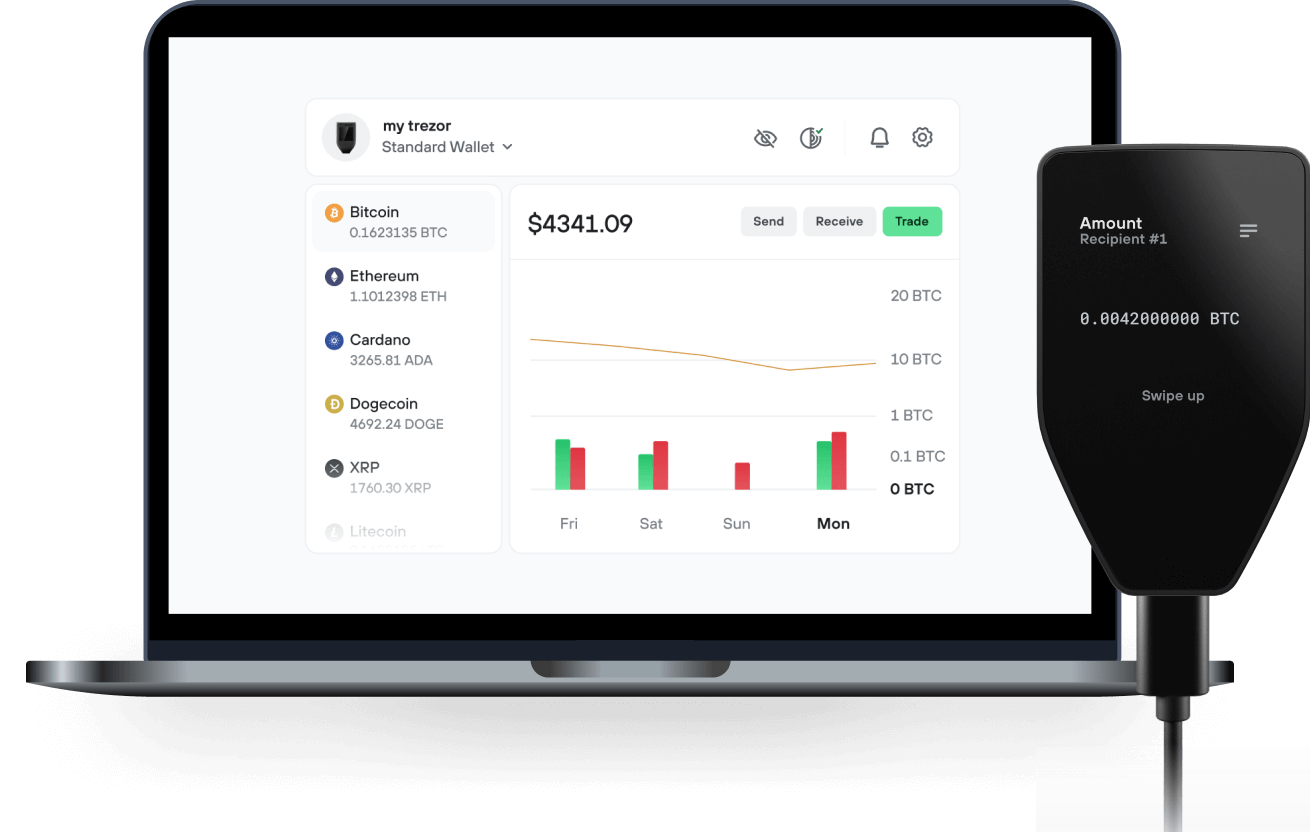
Send & receive your ZKEncrypt AI with the Trezor Suite app

Send & receive
Trezor hardware wallets that support ZKEncrypt AI
Sync your Trezor with wallet apps
Supported ZKEncrypt AI Network
Why a hardware wallet?
Go offline with Trezor
- You own 100% of your coins
- Your wallet is 100% safe offline
- Your data is 100% anonymous
- Your coins aren’t tied to any company
Online exchanges
- If an exchange fails, you lose your coins
- Exchanges are targets for hackers
- Your personal data may be exposed
- You don’t truly own your coins
How to ZKE on Trezor
Connect your Trezor
Open a third-party wallet app
Manage your assets
Make the most of your ZKE
Trezor keeps your ZKE secure
 Protected by Secure Element
Protected by Secure ElementThe best defense against both online and offline threats
 Your tokens, your control
Your tokens, your controlAbsolute control of every transaction with on-device confirmation
 Security starts with open-source
Security starts with open-sourceTransparent wallet design makes your Trezor better and safer
 Clear & simple wallet backup
Clear & simple wallet backupRecover access to your digital assets with a new backup standard
 Confidence from day one
Confidence from day onePackaging & device security seals protect your Trezor’s integrity
ZKEncrypt AI is a decentralized application (DApp) platform engineered to serve as a high-fidelity reference implementation for privacy-preserving AI computation on the Solana blockchain. This project provides the definitive architecture for integrating advanced, confidential compute paradigms within a high-throughput Web3 ecosystem.
The platform's core thesis is that the future of on-chain AI necessitates absolute data confidentiality. ZKEncrypt AI achieves this by implementing a robust Fully Homomorphic Encryption (FHE) infrastructure. This enables AI agents to perform complex computations—such as inference or data analysis—directly on user-supplied ciphertext. At no point in the compute lifecycle is the underlying plaintext data exposed to the AI model, node operators, or any network-level observers.