Safe & secure Zero wallet
Take control of your Zero assets with complete confidence in the Trezor ecosystem.
- Secured by your hardware wallet
- Use with compatible hot wallets
- Trusted by over 2 million customers
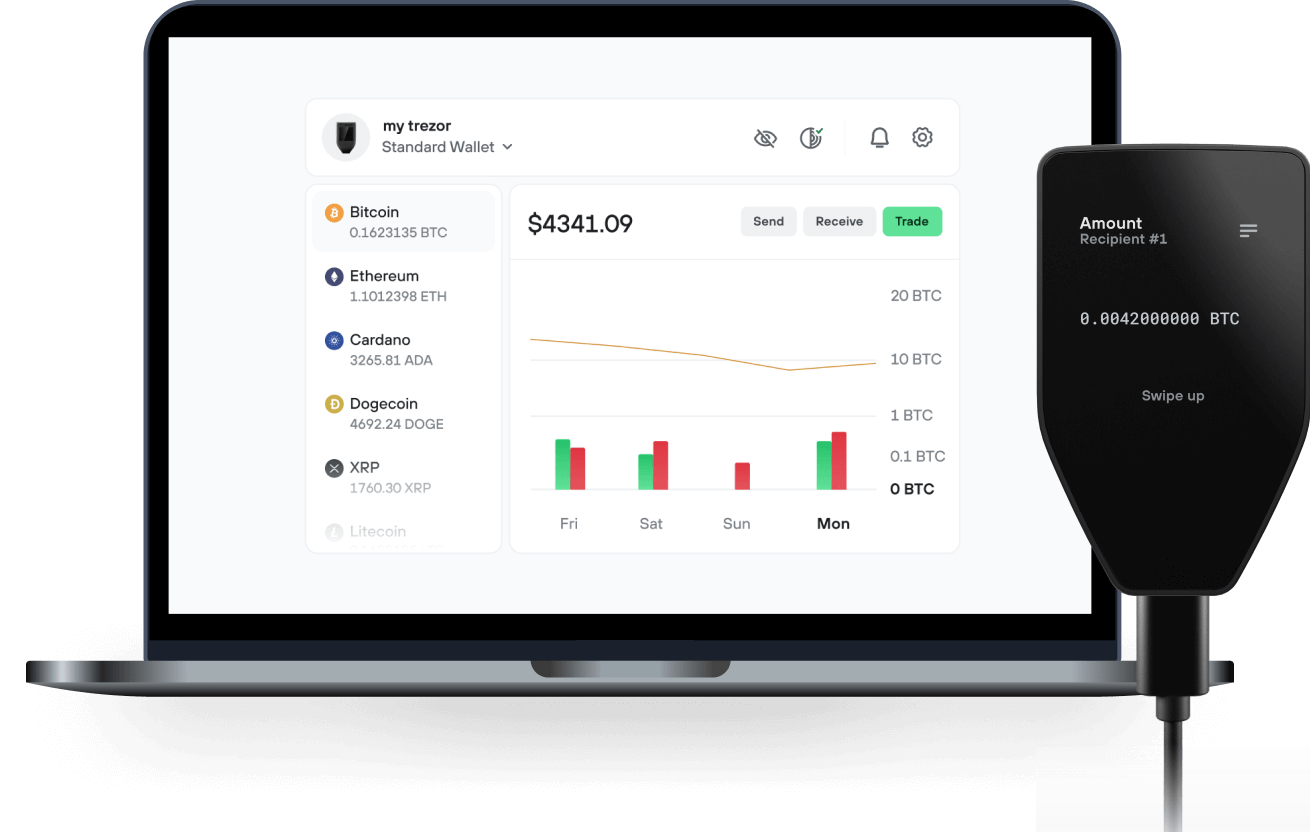
Send & receive your Zero with the Trezor Suite app

Send & receive
Trezor hardware wallets that support Zero
Sync your Trezor with wallet apps
Supported Zero Network
Why a hardware wallet?
Go offline with Trezor
- You own 100% of your coins
- Your wallet is 100% safe offline
- Your data is 100% anonymous
- Your coins aren’t tied to any company
Online exchanges
- If an exchange fails, you lose your coins
- Exchanges are targets for hackers
- Your personal data may be exposed
- You don’t truly own your coins
How to ZERO on Trezor
Connect your Trezor
Open a third-party wallet app
Manage your assets
Make the most of your ZERO
Trezor keeps your ZERO secure
 Protected by Secure Element
Protected by Secure ElementThe best defense against both online and offline threats
 Your tokens, your control
Your tokens, your controlAbsolute control of every transaction with on-device confirmation
 Security starts with open-source
Security starts with open-sourceTransparent wallet design makes your Trezor better and safer
 Clear & simple wallet backup
Clear & simple wallet backupRecover access to your digital assets with a new backup standard
 Confidence from day one
Confidence from day onePackaging & device security seals protect your Trezor’s integrity
A Privacy-Native Ecosystem
Zer0 is a privacy-first ecosystem built end to end for real adversarial conditions. From hardware and compute to cryptography and execution, the stack is designed so sensitive data never leaves your device and identity is never exposed.
The browser is the first surface. Beneath it sits a vertically integrated system combining on-device AI, zero-knowledge proofs, private routing, and verifiable execution. This allows users and agents to browse, transact, and act privately without relying on trusted intermediaries or opaque cloud assumptions.
Using Zer0 earns $ZER0. Rewards flow back into the network, auto-staked into mixnodes and execution workflows that secure the system and enable future applications. Brands gain measurable reach without surveillance. Users remain unseen by design.
Privacy becomes infrastructure.