Safe & secure Messiah wallet
Take control of your Messiah assets with total confidence in the Trezor ecosystem.
- Secured by your hardware wallet
- Use with compatible hot wallets
- Trusted by over 2 million customers
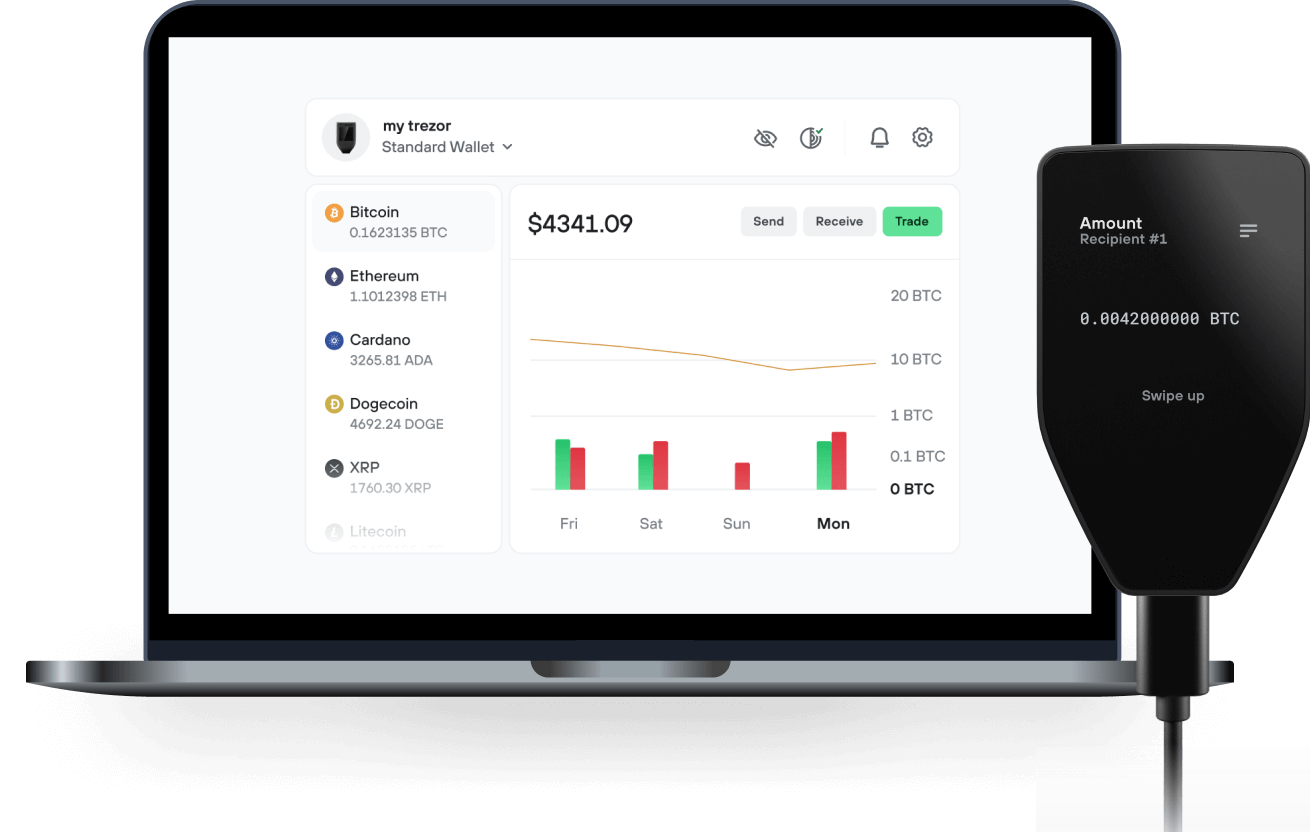
Send & receive your Messiah with the Trezor Suite app

Send & receive
Trezor hardware wallets that support Messiah
Sync your Trezor with wallet apps
Supported Messiah Network
Why a hardware wallet?
Go offline with Trezor
- You own 100% of your coins
- Your wallet is 100% safe offline
- Your data is 100% anonymous
- Your coins aren’t tied to any company
Online exchanges
- If an exchange fails, you lose your coins
- Exchanges are targets for hackers
- Your personal data may be exposed
- You don’t truly own your coins
How to MSIA on Trezor
Connect your Trezor
Open a third-party wallet app
Manage your assets
Make the most of your MSIA
Trezor keeps your MSIA secure
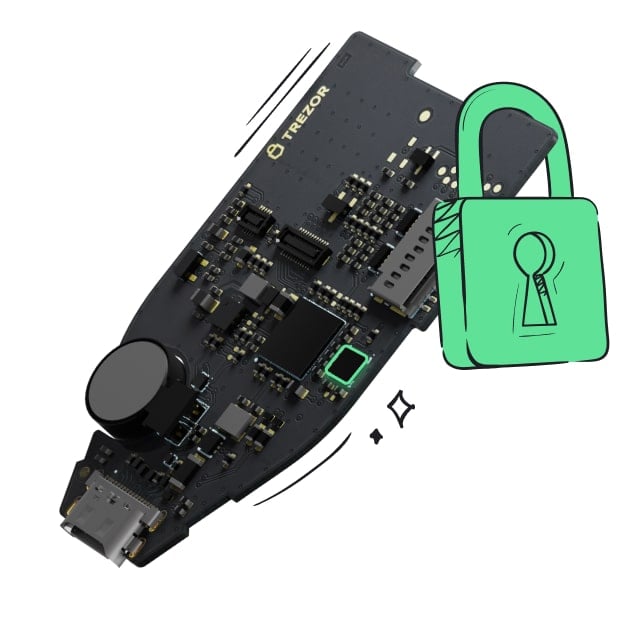 Protected by Secure Element
Protected by Secure ElementThe best protection against both online and offline threats
 Your tokens, your control
Your tokens, your controlAbsolute control over every transaction with on-device confirmation
 Security begins with open-source
Security begins with open-sourceA transparent wallet design makes your Trezor better and safer
 Clear & simple wallet backup
Clear & simple wallet backupRecover access to your digital assets with a new backup standard
 Confidence from day one
Confidence from day onePackaging & device security seals protect your Trezor’s integrity
The complexity and resource-intensive nature of deploying and managing web3 infrastructure present significant barriers to entry for many users; from a financial and technical perspective. Messiah aims to address these challenges by offering user-friendly, one-click deployment tools and automated management services for nodes, smart contracts, decentralised application and crypto mining operations. In simplifying these processes, we make the relevant infrastructure accessible to a broader audience, promoting widespread adoption of web3.
Messiah’s Mission
Current centralized systems face significant challenges, necessitating a reassessment of traditional approaches. Once the backbone of the digital revolution, centralized infrastructure now exposes vulnerabilities, creating single points of failure that increase the risks of cyberattacks and downtime. These vulnerabilities compromise internet services and data integrity. As the digital ecosystem grows more complex, the fragility of centralized systems becomes increasingly apparent. Messiah recognizes the urgent need for robust security measures to protect against unauthorized access and security breaches.