Safe & secure Impossible Cloud Network Token wallet
Take control of your Impossible Cloud Network Token assets with total confidence in the Trezor ecosystem.
- Secured by your hardware wallet
- Use with compatible hot wallets
- Trusted by over 2 million customers
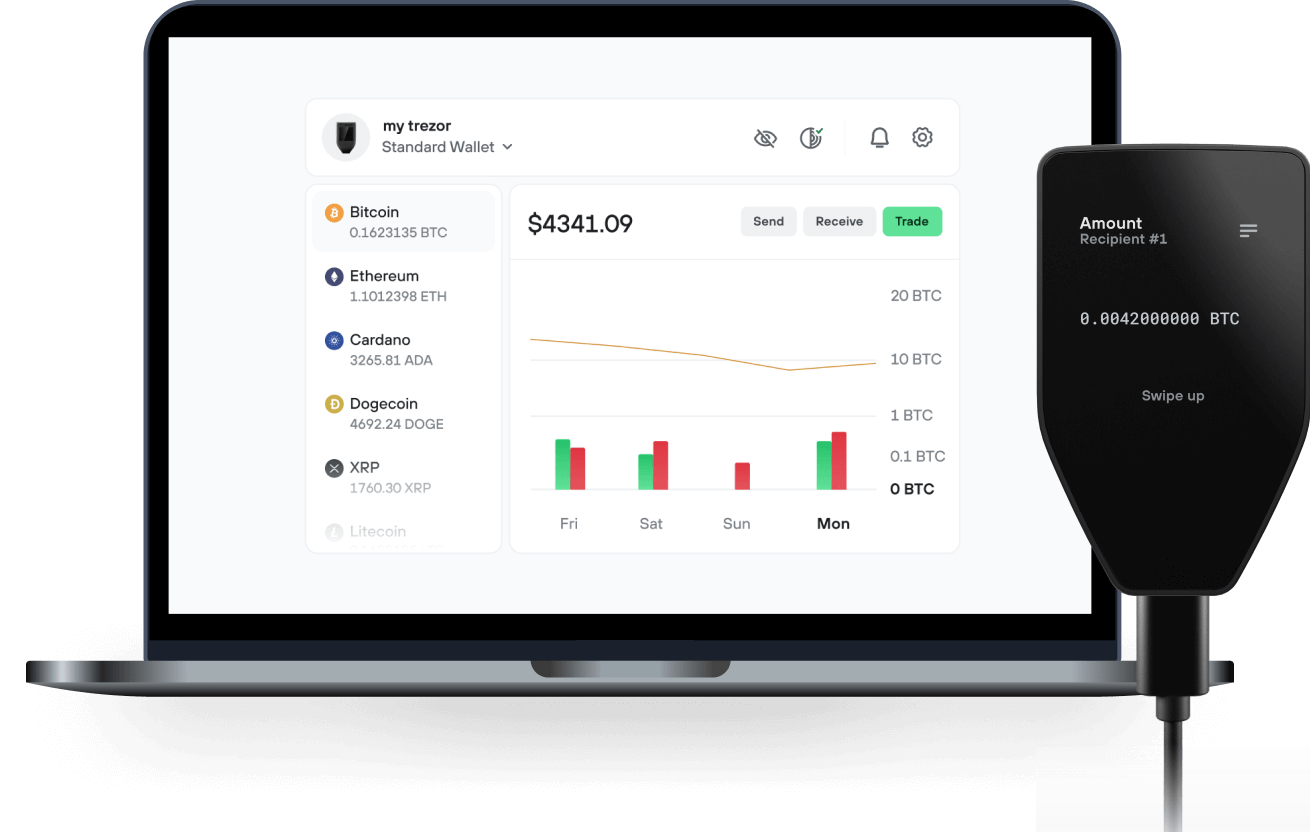
Send & receive your Impossible Cloud Network Token with the Trezor Suite app

Send & receive

Swap
Trezor hardware wallets that support Impossible Cloud Network Token
Sync your Trezor with wallet apps
Manage your Impossible Cloud Network Token with your Trezor hardware wallet, compatible with multiple wallet apps.
Trezor Suite
MetaMask
Rabby
Supported Impossible Cloud Network Token Networks
- Base
- Ethereum
Why a hardware wallet?
Go offline with Trezor
- You own 100% of your coins
- Your wallet is 100% safe offline
- Your data is 100% anonymous
- Your coins aren’t tied to any company
Online exchanges
- If an exchange fails, you lose your coins
- Exchanges are targets for hackers
- Your personal data may be exposed
- You don’t truly own your coins
How to ICNT on Trezor
Connect your Trezor
Install Trezor Suite app
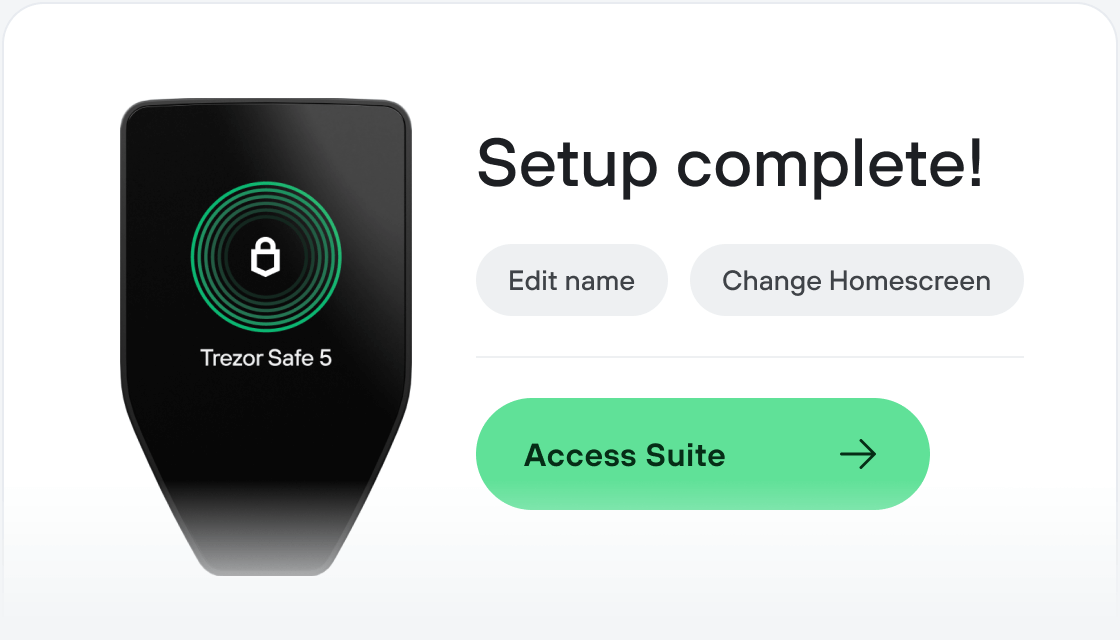
Transfer your ICNT
Make the most of your ICNT
Trezor keeps your ICNT secure
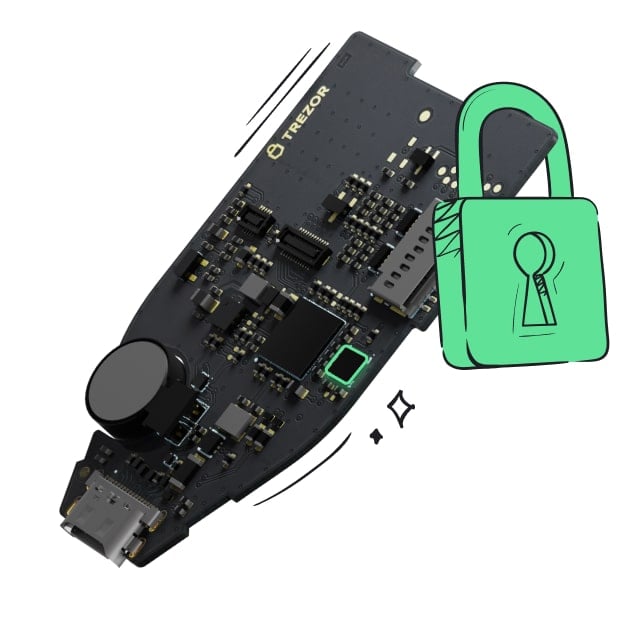 Protected by Secure Element
Protected by Secure ElementThe best protection against both online and offline threats
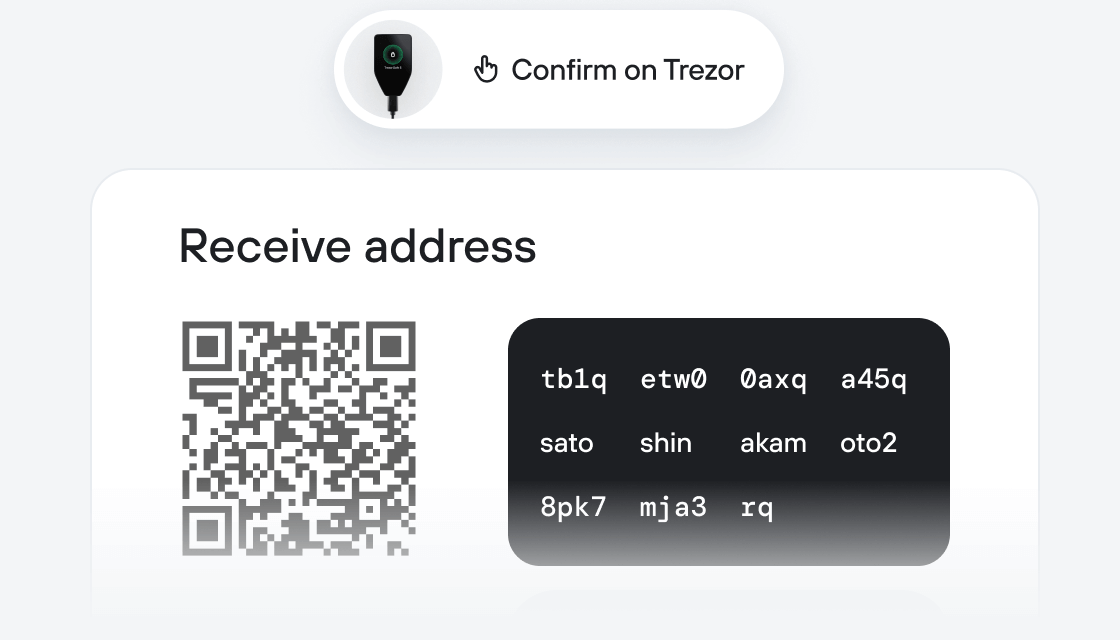
 Your tokens, your control
Your tokens, your controlAbsolute control over every transaction with on-device confirmation
 Security begins with open-source
Security begins with open-sourceA transparent wallet design makes your Trezor better and safer
 Clear & simple wallet backup
Clear & simple wallet backupRecover access to your digital assets with a new backup standard
 Confidence from day one
Confidence from day onePackaging & device security seals protect your Trezor’s integrity
Impossible Cloud Network (ICN) is a decentralized infrastructure protocol that provides enterprise-grade cloud services including storage, compute, and networking. Built as a multi-service DePIN platform, ICN enables hardware providers to contribute resources and service providers to access them using the native token ICNT. The network supports real-world enterprise use cases and is designed to offer high performance, security, and censorship resistance. ICNT is used for collateral by node operators, access to resources by service providers, and staking by the community to secure and participate in the protocol.