Billetera KAGE NETWORK segura y protegida
Toma el control de tus KAGE NETWORK activos con total confianza en el ecosistema de Trezor.
- Protegido por tu billetera física
- Usa con billeteras digitales compatibles
- Con la confianza de más de 2 millones de clientes
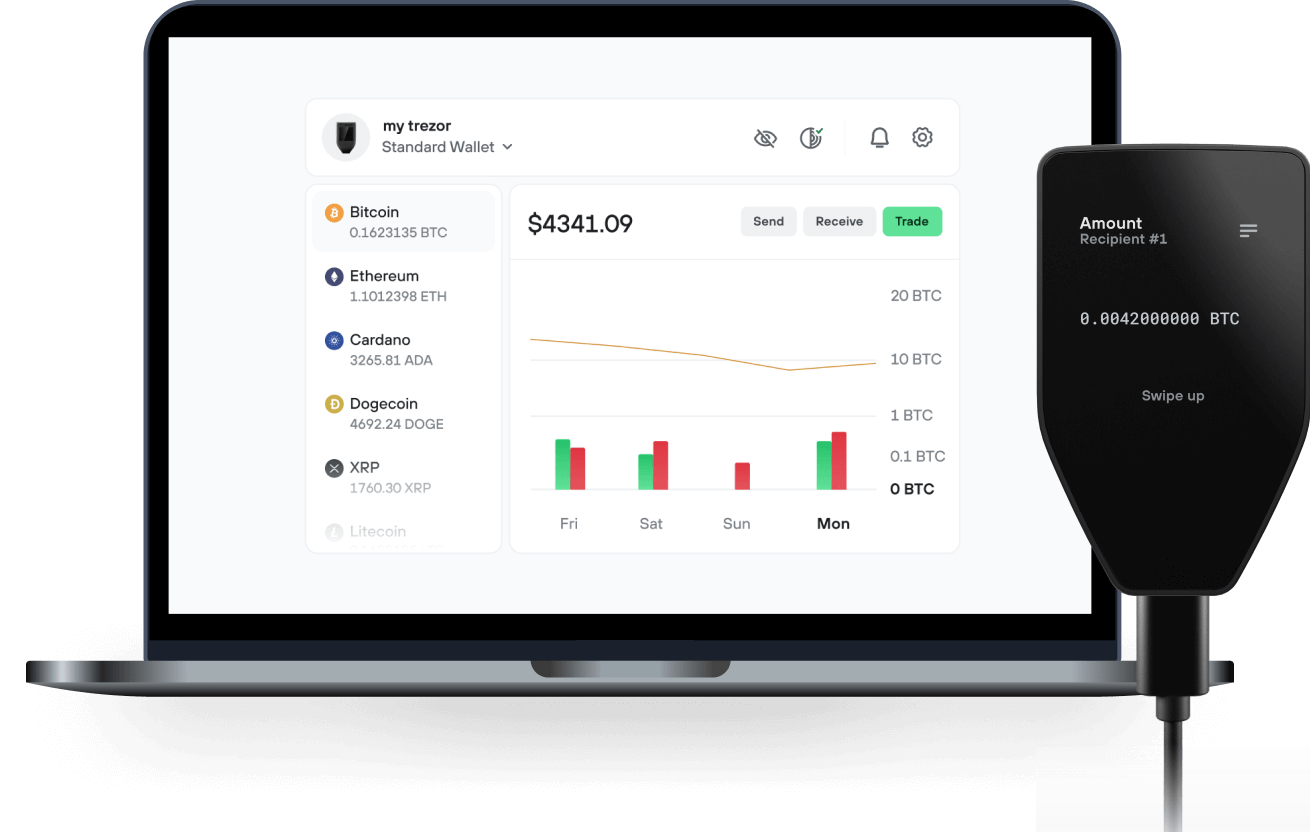
Envía y recibe tu KAGE NETWORK con la app Trezor Suite

Enviar y recibir
Billeteras físicas Trezor compatibles con KAGE NETWORK
Sincroniza tu Trezor con apps de billeteras
Gestiona tus KAGE NETWORK con tu billetera física Trezor sincronizada con apps de billeteras.
Trezor Suite
MetaMask
Rabby
Red KAGE NETWORK Compatible
- Ethereum
¿Por qué una billetera física?
Desconéctate con Trezor
- Tus monedas son 100% tuyas
- Tu billetera está 100% segura offline
- Tus datos son 100% anónimos
- Tus monedas no están atadas a una compañía
Exchanges en línea
- Si un exchange falla, pierdes tus monedas
- Los exchanges son blanco de los hackers
- Tu información personal puede ser expuesta
- Tus monedas no son realmente tuyas
¿Cómo usar KAGE en Trezor?
Conecta tu Trezor
Abre una app de billetera de terceros
Gestiona tus activos
Aprovecha al máximo tus KAGE
Trezor mantiene tus KAGE seguros
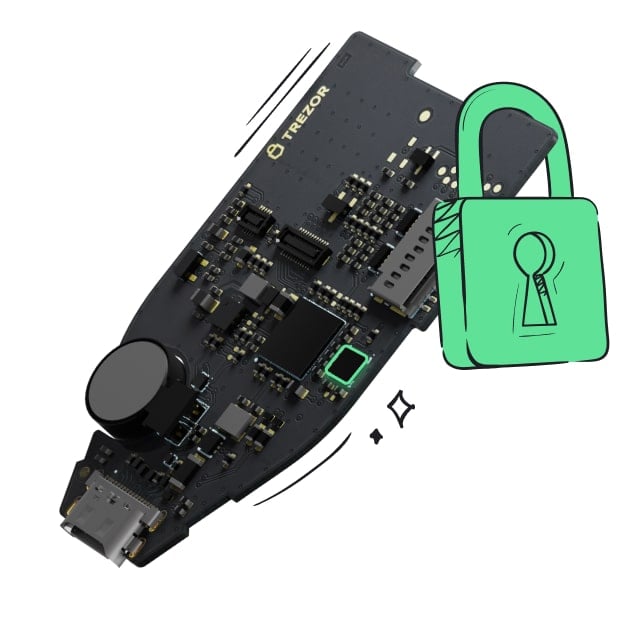 Protegido por Elemento Seguro
Protegido por Elemento SeguroLa mejor defensa contra amenazas tanto online como offline
 Tus tokens, bajo tu control
Tus tokens, bajo tu controlControl absoluto de cada transacción con confirmación directa en el dispositivo
 La seguridad empieza por código abierto
La seguridad empieza por código abiertoUn diseño de billetera de forma transparente hace que tu Trezor sea más seguro y confiable
 Copia de seguridad de billetera clara y sencilla
Copia de seguridad de billetera clara y sencillaRecupera el acceso a tus activos digitales con nuevo estándar de copia de seguridad
 Confianza desde el primer día
Confianza desde el primer díaEl embalaje y los sellos de seguridad del dispositivo protegen la integridad de tu Trezor
Building The Hardware Layer Of The Privacy-Focused Online Economy With A Battle-Tested Decentralized VPN Router Solution
With the unprecedented scale of digital data collection, increasingly sophisticated cyber threats, and ever-present government overreach, online privacy has never been more important. The proliferation of smart devices, IoT infrastructure and AI software is only set to amplify online risks by creating numerous new entry points for potential breaches. This has led to skyrocketing demand for privacy solutions, with the privacy-enhancing technology market forecast to exceed $24b by 2024.
VPNs (Virtual Private Networks) have emerged as a leading solution for online privacy due to their ability to encrypt internet traffic and mask users' IP addresses, effectively shielding personal data from prying eyes. This makes VPNs a reliable method for maintaining anonymity and protecting sensitive information. Indeed, adoption of VPNs has become so widespread that a recent Forbes report found that 33% of internet users worldwide have a VPN.
However, the current generation of centralized, software-based VPNs are replete with vulnerabilities and inefficiencies that limit their effectiveness as a long-term solution for delivering online security and privacy at scale. Software-based VPNs were designed with a single device - usually a personal computer - in mind. They struggle to handle the multi-device connected homes that users now find themselves in, which can include connected TVs, fridges, cameras and an ever growing list of IoT devices. Meanwhile, whilst early adopters were comfortable working with abstract software, mainstream consumers are seeking a simpler, plug and play solution. In addition to this, centralized VPN business models concentrate control and access to vast amounts of sensitive user data in the hands of a single entity. This creates a single point of failure and also opens up the possibility of governments compelling them to share data.

