Bitte beachten: Unsere Blogartikel sind derzeit nur auf Englisch verfügbar.

Introducing Tropic Square — Why transparency matters
In 2012 we brought you Trezor — the first hardware wallet, creating a brand new industry. Since the beginning, we’ve built our product on a very strong philosophy — let’s be as open as possible, let our customers have as much information as possible, so they can always make informed decisions for themselves. We still believe that was the right choice.
Recently, there were lots of discussions about the terms “Open-Source” and “Secure Element”, but these two terms were quite often misrepresented. Let’s have a look at what they really mean.
The Beauty of Open-Source
For some people, the term “open-source” means that software is free of charge. However, this term stands for much more than that. Open-source means that anyone is welcome to study, modify, distribute, and build on top of the software.
This is especially critical in the context of Bitcoin where we need to fully understand how everything works in order to build a truly decentralized system providing self-sovereignty and independence for its users. There is no other way to break free from governmental institutions, centralized banking, and so on.
Seeing Trezor as an integral part of the Bitcoin ecosystem, we wanted to stay truthful to this vision of breaking free. That’s why we are continuously advocating for the freedom open-source provides. We believe when it comes to your security, you shouldn’t be required to trust anyone and you should be able to verify everything.
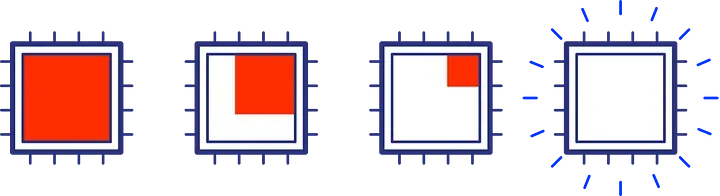
In our efforts to build a truly open hardware wallet, we tried to expand the trustless part as much as possible. We partly succeeded in removing us from the trust equation by creating open-source software and open-source hardware, but this effort is not currently possible to the full extent. At some point, the poetic ideals meet the real world. The world, which lacks transparency and in which various pieces of information are kept proprietary by their gate-keepers, makes it very hard to invite independent experts for review.
In this world, there is a special category of chips called “Secure Element” claiming to be secure, because they have received lots of certifications. They offer physical guarantees, but they do this at the price of the aforementioned lowered transparency and increased required trust. We decided to avoid using these chips, so our solution would not depend on blind trust in a third party, but we paid the price too. For people that really need the physical security of the chip, we came up with the mitigation — “a passphrase” that is entered at the start of the device, splitting the secret into two — one stored in the device and another one stored in the head of the user. However, this makes the user experience a little bit worse because users now have to remember and enter the passphrase.
Ideally, we would want the physical guarantees of Secure Element without the need to trust the chip vendor. But you might ask, what’s wrong with trusting the chip vendor? They have various certifications after all, right? Well, here’s why …
Why Certifications are Wrong
Current certifications such as Common Criteria discriminate against free and open-source development models. The reason is, they were developed before the rise of open source, so they don’t credit mass peer review and the detailed code review. What’s even worse is that certifications test only against a known set of predefined scenarios. Behavior outside of these scenarios is not tested at all and declared out of the scope of certification. However, that’s exactly the area where hackers operate!
Government policies assume projects without certifications are not secure, requiring a vendor to pay hundreds of thousands of dollars to get certified. These policies exclude independent companies and open-source initiatives from being used in professional areas.
This in effect causes companies to have very little motivation to undergo independent audits from security specialists; all they need is to get certified. Having all these certifications is ultimately just an easy business and marketing strategy.
Most, if not all, Secure Element vendors require you to sign the NDA (non-disclosure agreement) in case you want to access documentation of their chips. Some of them even require you to do so even if you only want to buy their chips, so there is no way you can obtain one without signing the NDA.
Our Dive into Secure Element, NDA chips and how we broke them Even though we did not believe in Secure Element and security by NDAs, over the seven years we have investigated Secure Element as much as everybody else. We even came up with a Trezor model containing a Secure Element. However, we only confirmed our assumptions and saved us and our customers lots of future trouble.
In one of the many options we reviewed, we saw a potential candidate for a Secure Element to be used in our product and we went deeper into our research. As this was a Common Criteria certified chip, we did not expect what we found. Over a few weeks, we uncovered several different critical flaws requiring no special hardware leading to the extraction of the secrets from the chip. We quickly realized these were the attacks nobody tested against. Not the vendor, nor any certification party that provided the certifications.
We started to plan a responsible disclosure and reported these issues to the vendor. During the call with the management that followed, we learned the vendor will not communicate the vulnerabilities to their customers and we won’t be able to tell the world about these critical mistakes either, because of the NDA we were forced to sign to get the full documentation of the chip.
We did not even try very hard to break the chip and if we managed to do it, we are sure somebody else could do it too. However, they are not able to divulge this either, because of the infectious nature of the NDAs.
When we asked the company if they were interested in a full audit of the chip performed by us, we were laughed at, because doing so will not give the vendor any official certification the government policies and organizations are after.
To summarize: not only are the current certifications not very useful, because of their very limited guarantees; but also NDAs are very bad, because of their infectious nature of withholding information. This is all happening because the incentives of the hardware vendors are not aligned with the incentives of their users and the hardware vendors don’t hesitate to use every possible way to protect their needs before the needs of their users.
Introducing Tropic Square
In order to ultimately fulfill our original hardware wallet vision, we need an open, fully auditable, chip. We come from the Bitcoin background, where the emphasis on “Don’t Trust, Verify” is very strong, but thinking further we realized this is a pressing issue not only for HW wallets manufacturers, but it is important for any hardware manufacturer (or their customers) that requires transparent security. The security that can and should be audited by the wide community of security experts. Any industry where gatekeepers are not welcome. Internet of Things, Secure Boot you name it.
We all deserve to live in a better world and it’s time to fix it here and now. We are very well aware we are not able to do it by ourselves. That’s why we have invited the best people in the field we know: Evžen Englberth (CEO), an expert with more than 18 years of experience in the field of Electronic Manufacturing Services (EMS) and a former sales director for Jablotron Group, and Jan Pleskač (CTO) an experienced ASIC/FPGA design architect and application engineer with a demonstrated history of working for brands like Intel and S3 Group.
Together, we are building a new company: Tropic Square, the creators of the next TRuly OPen Integrated Circuit. This new entity’s purpose is to deliver a chip as open-source as possible. The goal is to provide access to design specifications, verification, and testing without obscurity. There is also work to be done on physical implementation, to make the chips secure, yet transparent and verifiable by anyone. If you are interested in knowing more or you want to join forces with our team — go to our webpage tropicsquare.com and let us know.


