Bitte beachten: Unsere Blogartikel sind derzeit nur auf Englisch verfügbar.
Google just changed the quantum deadline. Here's what it means for your bitcoin…
Quantum computing is no longer just a distant threat to Bitcoin. Google’s latest research suggests that breaking Bitcoin’s cryptography may require far fewer resources than previously thought, but it’s still theoretical. No such machine exists today. The real challenge isn’t immediate risk, but community coordination. Preparing Bitcoin for a post-quantum world will take time, consensus, and action long before the threat becomes real. The new Trezor Safe 7 is the first hardware wallet with quantum-ready protections.
The quantum threat to Bitcoin used to be registered as FUD. Today? It’s become a legitimate concern for the future of crypto, especially in light of Google’s recent whitepaper, which suggests that breaking Bitcoin’s cryptography may require around 500,000 physical qubits… that’s roughly a 20x reduction from previous estimates. Should we be worried?
TL;DR, no, we don’t need to panic. But yes, the industry should be preparing for a quantum future because it’s no longer just science fiction. Trezor has taken steps forward with the first-ever quantum-ready Trezor Safe 7, but before hardware wallets can truly be quantum-proof, more is needed.
What actually is a quantum computer? A simple explanation…
So basically, it's a computer that solves certain problems much faster than traditional computers because it works completely differently.
If you want a slightly (very slightly) deeper understanding, here are two words you need to know:
Bit: The smallest unit of information in a traditional computer. It can be either 0 or 1. Qubit: The quantum version of a bit. It can be 0, 1, or both at the same time.
This might help you understand qubits better:
“The best analogy I’ve heard is that of spinning a coin on a table. It’s neither heads nor tails until it stops. While spinning it’s both heads and tails at the same time.” - Matthew Mariani’s Quantum Journey Blog
While a normal computer works through possibilities one by one, a quantum computer can work with many possibilities at the same time, which is what makes it so powerful for certain types of complex problems.
That does not mean quantum computers are simply faster versions of normal computers. It means they solve certain kinds of problems in a completely different way. So while classical computers process information in clear, fixed states, quantum computers operate in multiple states simultaneously, which are not fixed. It’s a strange middle ground that could eventually transform how we solve problems that are far too complex for today’s machines.
Quantum computers can’t magically solve everything and are not automatically superior, but there are certain algorithms that they can solve extremely effectively. One of the algorithms they can affect is the digital signature algorithm used by Bitcoin.
This isn’t just a Bitcoin problem though. Cryptography is everywhere and is the backbone of modern digital life, so the creation of a quantum computer is a challenge for a lot of fields beyond Bitcoin and crypto…
- E-commerce
- Classified documentation
- Software updates
- Payments
- Messaging
… even government and army communications! So a cryptographically relevant quantum computer could indeed break many things if society is not ready with post-quantum protections.
Bitcoin’s quantum challenge
While being ready for a post-quantum world is important for many industries, Bitcoin is slightly different because its main strength (being decentralized) is also a challenge. In this case, it’s harder to get a global consensus on how to proceed.
Cloudflare reports that over 50% of human-initiated traffic is now post-quantum safe, although the exact figure varies depending on whether bot traffic is included (Cloudflare is almost 20% of all internet websites). Yet, Bitcoin still doesn’t have a confirmed path.
The good news is that this is already being worked on and discussed as a community…
Bitcoin has two potential threats from quantum computing:
- Long exposure (bitcoins at rest)
This refers to bitcoins that have already been mined and stored on addresses. UTXOs with exposed public keys are vulnerable in a quantum scenario, as Shor's algorithm could derive the corresponding private key from a public key. This includes coins on older address types, reused addresses, and coins from spent Taproot outputs.
- Short exposure (unconfirmed bitcoin in transactions that are waiting for a miner to confirm the block)
In order to spend a transaction, you need to reveal the public key. Otherwise, the nodes can not verify the signature. They cannot do that without the appropriate public key.
This Bitcoin transaction is not yet part of the blockchain. It is currently in the mempool, being transmitted between nodes and waiting to be included by miners. Once a miner includes it in a valid block and the block is added to the blockchain, the transaction becomes confirmed. During this period, the transaction is publicly visible across the network, and any revealed public keys are temporarily exposed before the funds are assigned to a new address, making them potentially vulnerable to a quantum attack.
So, what needs to happen for Bitcoin to be ready for quantum computing?
Everyone will need to migrate to a new post-quantum address. This will take a long time to decide on the correct path and reach consensus.
What does Google’s recent whitepaper mean for Bitcoin’s security?
What makes Google Quantum AI Labs' research unique is that their paper estimates a Bitcoin private key could, in theory, be derived using a quantum computer in about nine minutes, using relatively low qubit and gate requirements compared to earlier work (fewer than half a million physical qubits in their model). This could affect both unconfirmed transactions in the mempool and previously mined coins tied to exposed public keys.
But, before we all panic, it’s important to remember that this is currently theoretical.
No such machine exists today. Google was clear about that.
The current state:
- Quantum Computers are still far away
- There are no relevant quantum computers as of today
- Even with Google’s lower estimates, today’s quantum computers have only hundreds to a few thousand physical qubits, far below the hundreds of thousands+ that would be needed in the recent paper’s model
Reasons to pay attention:
- The consequences are enormous
- Adopting new cryptography takes time
- This could break both Bitcoin and the internet as we know it (among other things)
But, how long is “still far away”?
Here’s an interesting chart from just 2024 on what the ‘experts’ think:
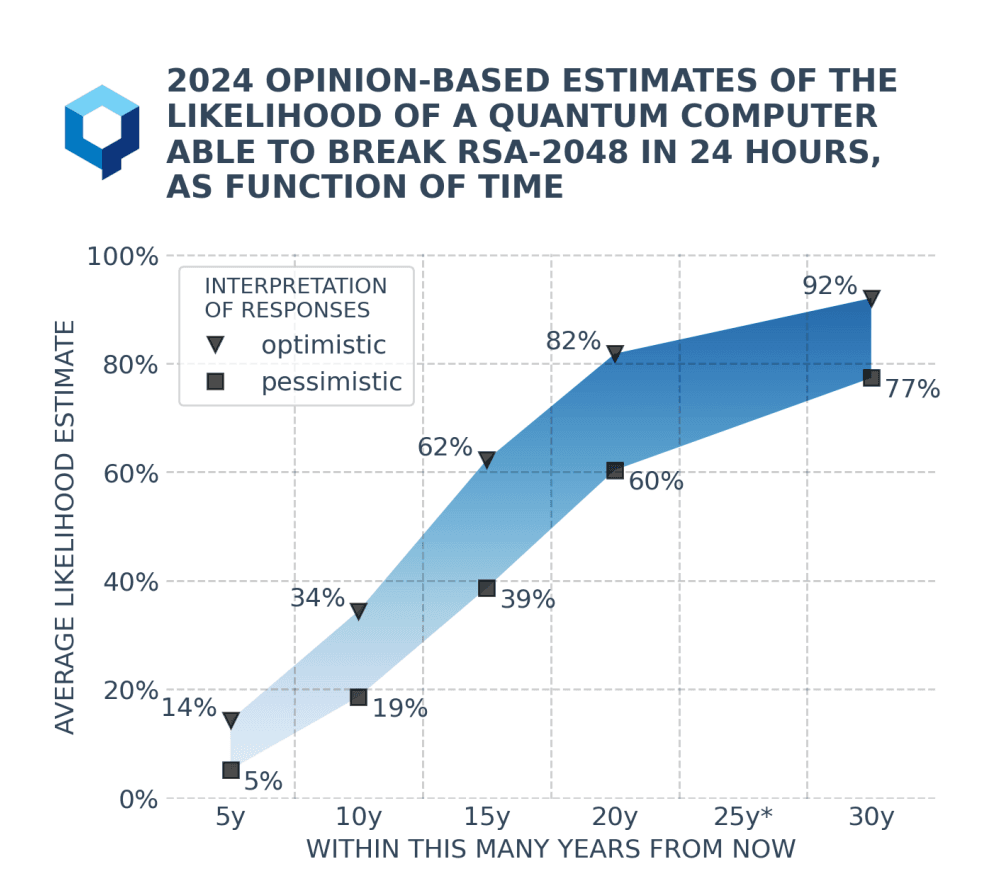
You’ll see that estimates above a 50% likelihood range between 15-20 years.
As for Google? They’ve set an internal deadline for migrating their services to post-quantum systems by 2029, which is quite soon given the estimated timeline above.
The problem with this chart is that it is from 2024 and a lot of progress has been made since. There’s a good chance that if these same people were asked again today, their answers would probably be revised to a few years earlier, if not more. This just shows how fast the technology is moving.
Companies like NordVPN, Apple, and many more have already started work on being post-quantum secure, so this is not uncharted territory and solutions are already quite mainstream.
The leading solution being explored for Bitcoin:
BIP 360 proposes a soft fork that introduces a new Bitcoin transaction type called Pay-to-Merkle-Root (P2MR). It is similar to Taproot, but removes the quantum-vulnerable option to spend via the traditional key path. The main goal of BIP 360 is to prepare for future post-quantum BIPs.
The design is intended to allow gradual adoption while remaining compatible with existing Bitcoin infrastructure. The idea of the BIP 360 authors is to follow up with another BIP that introduces more post-quantum algorithms.
But… what should be done with quantum-vulnerable coins?
Bitcoin in old wallets (like Satoshi’s coins) is vulnerable if quantum computers arrive because their public keys are exposed.
There are more aggressive proposals like the BIP 361 draft that essentially suggest ‘freezing’ these coins. It would effectively block funds that are not upgraded in time. Understandably, some users think this goes against the Bitcoin ethos, and it’s still being widely debated.
As for what we’re doing at Trezor to get ready as best we can:
Our new Trezor Safe 7 is quantum-ready. This means that the bootloader is prepared to accept quantum-safe updates.
Regardless of what each blockchain does individually, with this hardware wallet you’ll be ready to upgrade once the world goes quantum, rather than having to rush out and find a quantum-ready wallet before it’s too late. Learn more here.
Read Trezor CTO Tomáš Sušánka's full breakdown on our response to a quantum future:
What did Satoshi Nakamoto think about the threat of quantum computing to Bitcoin?
In 2010, Satoshi Nakamoto had this to say about quantum computing:
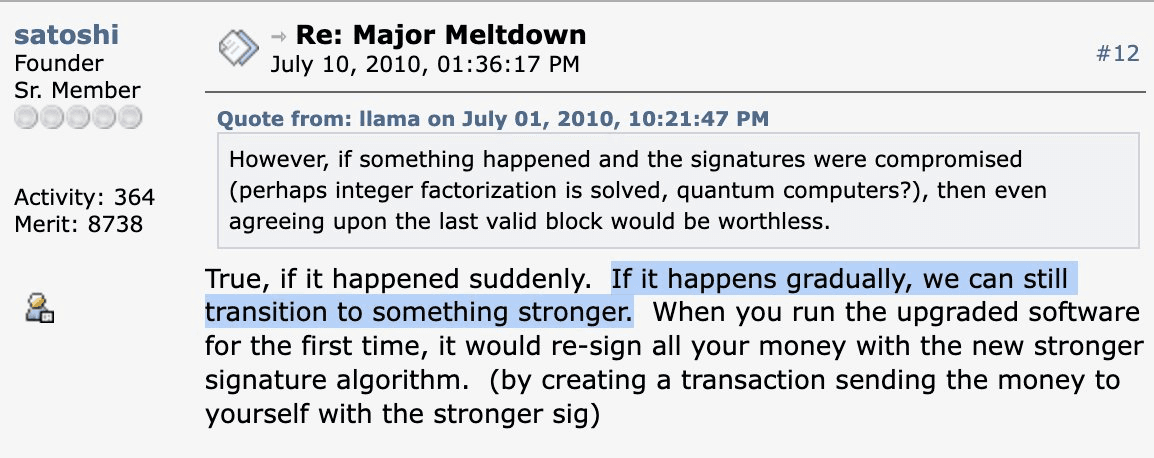
"If it happens gradually, we can still transition to something stronger."
Satoshi suggested that a gradual transition would make adaptation manageable. In practice, reaching consensus and moving users to post-quantum cryptography will take time. Bitcoin’s slow, deliberate governance is a strength, but it also makes rapid upgrades far harder than in centralized systems.
There is no single best path yet, but there is good progress and community discussions underway. Google’s research may accelerate this change (it has already sparked more interest and urgency around this topic).
Bitcoin & quantum FAQs
1. Can quantum computers break Bitcoin today? No. There is currently no quantum computer powerful enough to break Bitcoin’s cryptography. Google’s research is theoretical and highlights what could be possible in the future, not what’s possible today.
2. How far away is a real quantum threat? Most estimates still place a cryptographically relevant quantum computer at least 10–20 years away. However, progress is accelerating, which is why companies (and Bitcoin) are starting to prepare now rather than waiting. This is still theoretical, and timelines remain highly uncertain.
3. Which bitcoins are most at risk from quantum attacks? Coins with exposed public keys are the most vulnerable. This includes reused addresses, older address types, and coins that have already been spent from. Unconfirmed transactions may also have a short window of exposure while in the mempool.
4. What should Bitcoin users do right now? There’s no need to panic or take immediate action. The best approach today is to follow best practices: avoid address reuse and stay updated as post-quantum solutions are developed. Hardware wallets like the Trezor Safe 7 are beginning to prepare for this transition with quantum-ready protections.


